Cloud Hosting
Introduction
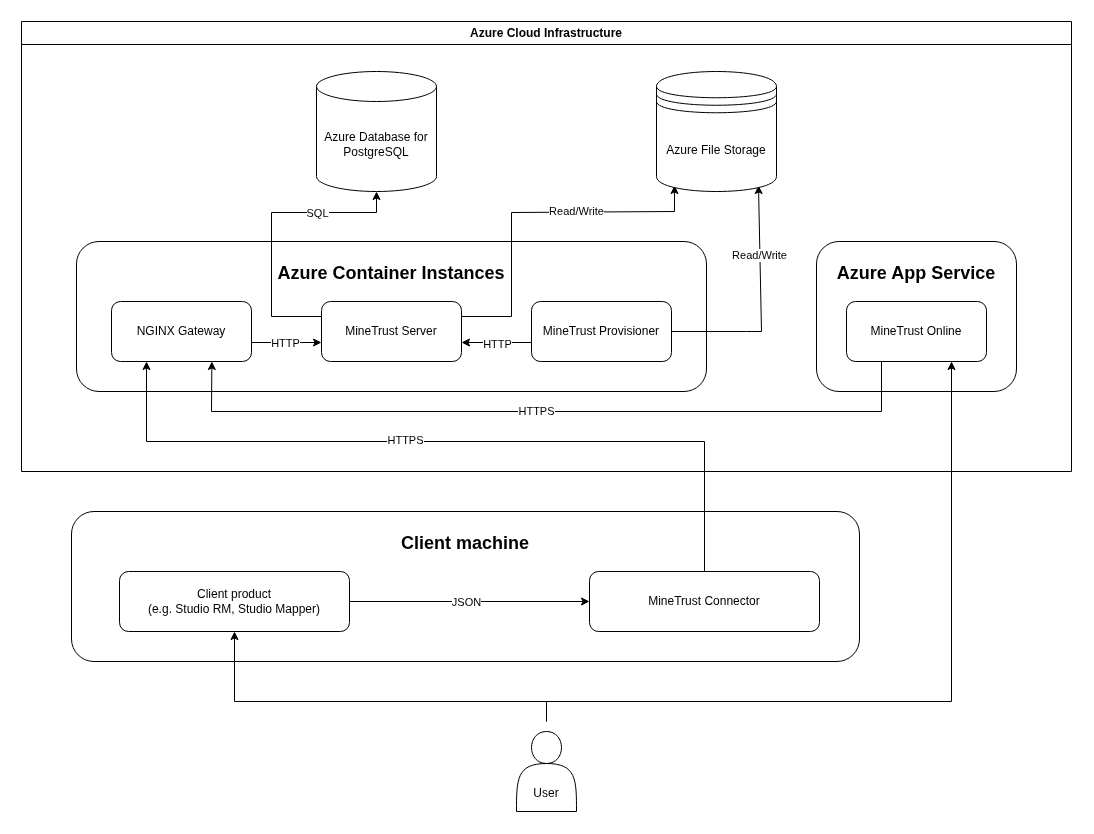
MineTrust can be hosted in the cloud using Microsoft Azure services. This architecture leverages Azure Container Instances (ACI) for compute, Azure File Storage for persistent storage, Azure App Service for a web frontend, and a PostgreSQL database backend.
Architecture Diagram
Architecture Components
Azure Container Instances (ACI) – Compute Layer
- ACI provides a scalable, serverless compute environment to host microservices and application workloads.
- Containers run stateless processing tasks, including data transformation, ingestion, and API services.
- Secure communication with other Azure services using managed identities and private networking.
See also https://learn.microsoft.com/azure/container-instances/container-instances-overview.
Sub-components
- MineTrust: Core business logic container which hosts the main MineTrust processes, and exposes functionality via a REST API.
- Provisioner: Sidecar container responsible for the automatic provisioning of entities within MineTrust.
- NGINX: Acts as a reverse proxy, handling incoming traffic, load balancing, and API gateway functionalities.
See MineTrust Server and MineTrust Provisioner for more information.
Azure File Storage – Persistent Storage Layer
- Provides the underlying persistent file storage to both the MineTrust and Provisioner container instances.
- Supports high availability and redundancy with geo-replication capabilities.
See also https://learn.microsoft.com/azure/storage/files/storage-files-introduction.
Azure Database for PostgreSQL – Database Layer
- Provides a database backend for the MineTrust relational data model.
- May optionally be enabled from high availability, automated backups, and disaster recovery features.
- MineTrust communicates with the database backend via Entity Framework.
See also https://azure.microsoft.com/products/postgresql.
Azure App Service – Web Frontend
- Hosts the user-facing web application for managing and visualizing data (informally 'MineTrust Online').
- Connects to MineTrust backend via the REST API.
See MineTrust Online for more information.
See also https://learn.microsoft.com/azure/app-service/overview.
Connectivity
The communication model of the MineTrust architecture is laid out as follows:
| Source | Destination | Protocol | Port | Description |
|---|---|---|---|---|
| MineTrust Connector | NGINX Gateway | HTTPS | 443 | MineTrust Connector synchronises data with MineTrust Server via the NGINX Gateway |
| NGINX Gateway | MineTrust Server | HTTP | 9000 | NGINX Gateway proxies incoming traffic to MineTrust Server on the same Azure Container Instance |
| MineTrust Provisioner | MineTrust Server | HTTP | 9000 | MineTrust Provisioner runs ETL -style jobs against MineTrust Server |
| MineTrust Server | Azure Database for PostgreSQL | SQL | 5432 | MineTrust Server reads and writes entity data to and from the PostgreSQL database |
| MineTrust Server | Azure File Storage | azurefile | N/A | Underlying file storage is mounted directly into the MineTrust Server application container using the 'Azure file' mount type, providing persistent storage to the application |
| User/browser | MineTrust Online | HTTPS | 443 | Users interact with the web application via a browser installed on their local machine |
| MineTrust Online | NGINX Gateway | HTTPS | 443 | MineTrust Online provides a user interface for interacting with files and folders via the MineTrust Server REST API and the NGINX proxy |
Redundancy/Disaster Recovery
The redundancy and disaster recovery aspects of the platform are facilitated by the corresponding features of the components considered as Azure resources. Some typical recommendations are as follows:
-
Database backups should be configured to run on a weekly basis.
-
File storage backups should be configured to run on a weekly basis.
-
Monitoring (Azure Insights) of the system should be enabled in order to alert on periods of high load and scale resources accordingly (e.g. Database tier, Storage access level etc.).
Security
- The MineTrust Online web application endpoint is automatically secured using Transport Layer Security (TLS) when deployed to Azure.
- HTTP traffic between MineTrust and its client components may optionally be secured using TLS (an appropriate certificate must be provided).
- Encryption support for data at rest may be facilitated via the capabilities provided natively by Azure for those resources.
Rollout
- Deployment of the MineTrust cloud platform is orchestrated using Azure Resource Manager (ARM) templates.
- ARM templates provide infrastructure-as-code (IaC) to ensure consistent, repeatable deployments across environments.
- The rollout process automates provisioning of ACI instances, Azure File Storage, PostgreSQL databases, and Azure App Service.
- Internally, we integrate the ARM templates into our continuous integration and deployment (CI/CD) system to ensure reliability and consistency of the platform.

